Some very generous people at work decided to offer me (for free!) Cisco ASA 5505 security appliance. Great isn’t it? Great indeed given ASAs are top class firewall devices.
Appliance itself has unlimited number of users (other options made by Cisco are 10 and 50 users based on internal to external VLAN connections) and its running security plus licensing model. Needless to say that’s about £500 worth of money!
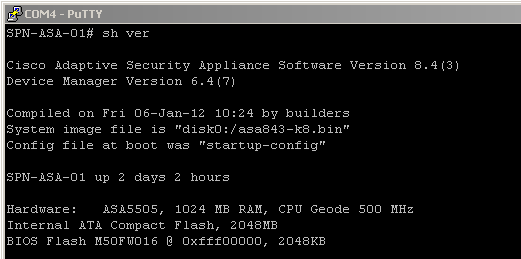
So moving to the ASA itself – model I have shipped with 512MB of RAM and 128MB CF card. Both of them modules can be upgraded to incorporate e-pen (RAM) and more space for historical data i.e. logs (CF card).
I just happen to have spare Integral IN1T1GNSKCX 1GB DD1 PC3200 (400 MHz) stick which, to my surprise, worked straight away! ASA didn’t have any issues detecting the new memory and booted up absolutely fine. There are lots of modules that won’t work full stop and quick search using your favourite search engine reveals that some people had tried 2-3 different sticks with no luck whatsoever. In my case completely random module worked first time. Awesome.
2GB compact flash card has been ordered from eBay and should turn up any day now so I will let you guys know how that goes. 2GB is the maximum that ASA can take, anything above will be most likely seen as 0MB so no point trying (it’s a limitation of FAT16 and cluster size not the ASA itself though). Card I have ordered is made by SanDisk and the exact model reads as ‘Ultra II 2GB 15MB/s’. USB CF card reader is also required so you can copy ASA firmware, ASDM and license file from old card to the new one.
So, for now, my ASA looks like this:
Continue reading →
Like this:
Like Loading...